Why human-centric fraud needs its own framework and what Charm is building to close the gap.
For twenty-five years, cybersecurity has run on a simple architectural bet: name a vulnerability, score it, patch it, defend against it. That bet built CVE, CVSS, CWE, and the vulnerability-management industry on top of them. It works because software has a structure we agreed to catalogue.
The human mind does not. And that's where our frameworks stop.
Today, most successful attacks don't exploit unpatched code: they exploit people. Verizon's DBIR has placed the "human element" inside more than 80% of breaches for years. Phishing, scams, business email compromise, account takeover through social engineering, the common thread is that the exploited asset is a person, not a system. There is still no CVE for a bail scam, no CVSS for an invoice fraud, no patch registry for a BEC wire transfer that rides an authority bias into a CFO's approval.
What F3 Gets Right
In 2025-2026, MITRE's Center for Threat-Informed Defense published the Fight Fraud Framework (F3), a deliberate extension of ATT&CK into the fraud domain. It gives defenders a shared, evidence-based vocabulary for how fraud actors operate, organized into seven sequential tactics (Reconnaissance, Resource Development, Initial Access, Defense Evasion, Positioning, Execution, Monetization).
It's the first MITRE-backed framework that treats fraud adversaries with the same taxonomic rigor ATT&CK applied to nation-state intruders. It is, for the fraud community, something close to a founding document. Any honest reading has to start there.
And Where It Stops
F3 is built from ATT&CK's lineage, which was designed to model attackers exploiting systems. In ATT&CK, the target is essentially passive: a server, a process, a credential store. It has no emotional state. It is not afraid, flattered, rushed, or under the influence of a fabricated family emergency.
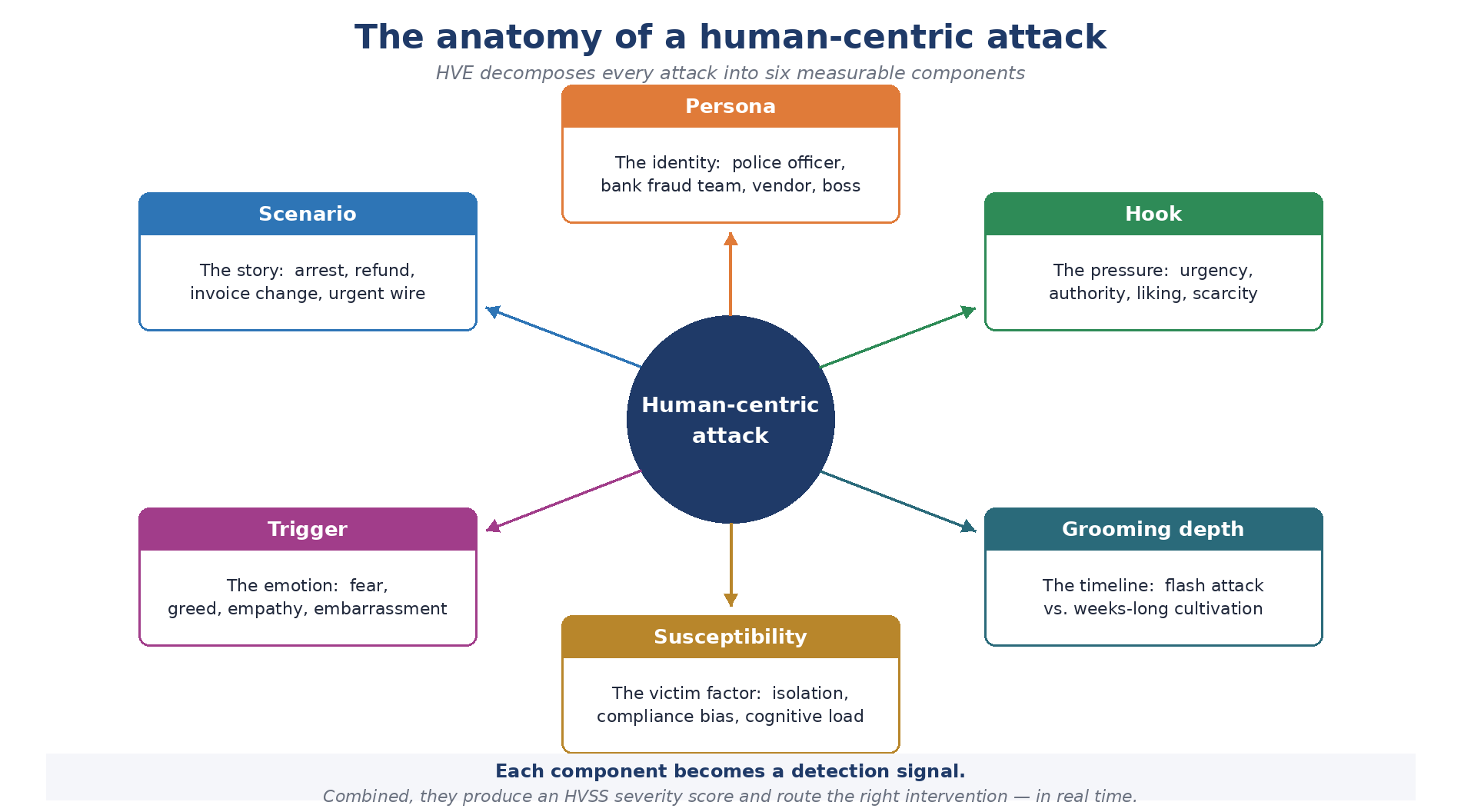
Human-centric fraud is different in kind. A person does not fail the way a buffer overflows. A person fails because an attacker identified a predisposing factor, delivered a plausible scenario, hooked an emotional lever, assumed a credible persona, and, often over time, deepened the victim's compliance until the transaction felt reasonable.
F3 captures the attacker's moves. It doesn't capture why those moves worked, who was vulnerable, how severe the specific combination is, what to do in the next sixty seconds, or what the victim needs after the money is gone. Those questions live on the victim side of the fraud equation, and they need a different kind of framework.
CVE secures servers. HVE secures humans.
The Gap: A Framework For Human-Centric Fraud
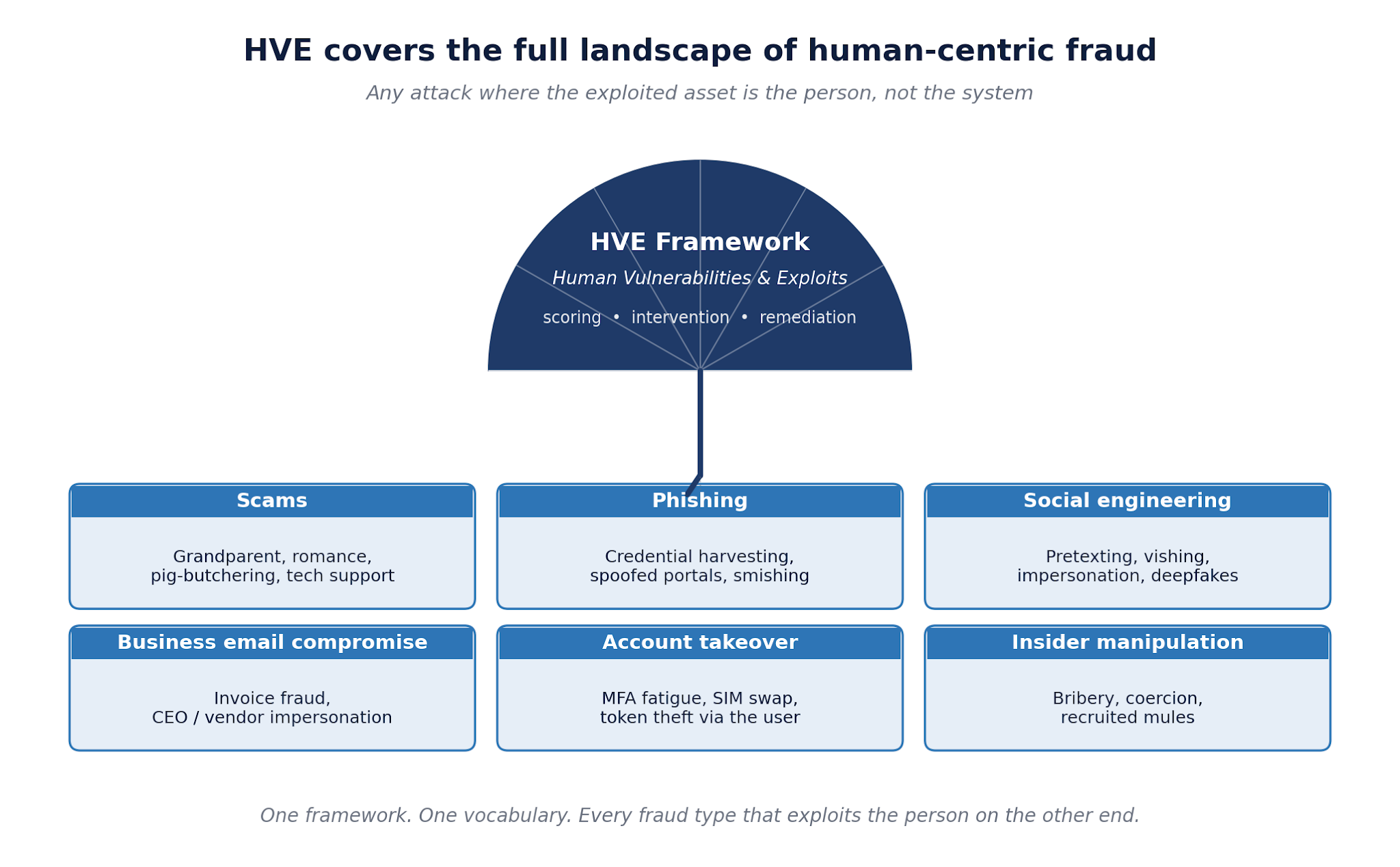
This is what Charm Security's Human Vulnerabilities & Exploits (HVE) framework is built to close. HVE is deliberately broader than "scams." It is the framework for human-centric fraud as a category, every attack where the exploited asset is the person on the other end.
That includes scams (bail, romance, pig-butchering, tech support), phishing (credential harvesting, spoofed portals, smishing), social engineering (pretexting, vishing, deepfake impersonation), business email compromise, account takeover that rides MFA fatigue or a social-engineered reset, and insider manipulation. Different channels, different payloads, one architectural reality: the vulnerability being exploited is human.
What HVE Adds On Top Of F3
HVE is not a replacement for F3. The two are complementary halves of a full-spectrum model: F3 maps the attacker, HVE maps the human being exploited. Deployed together, they give a fraud program a shared language from reconnaissance through remediation.
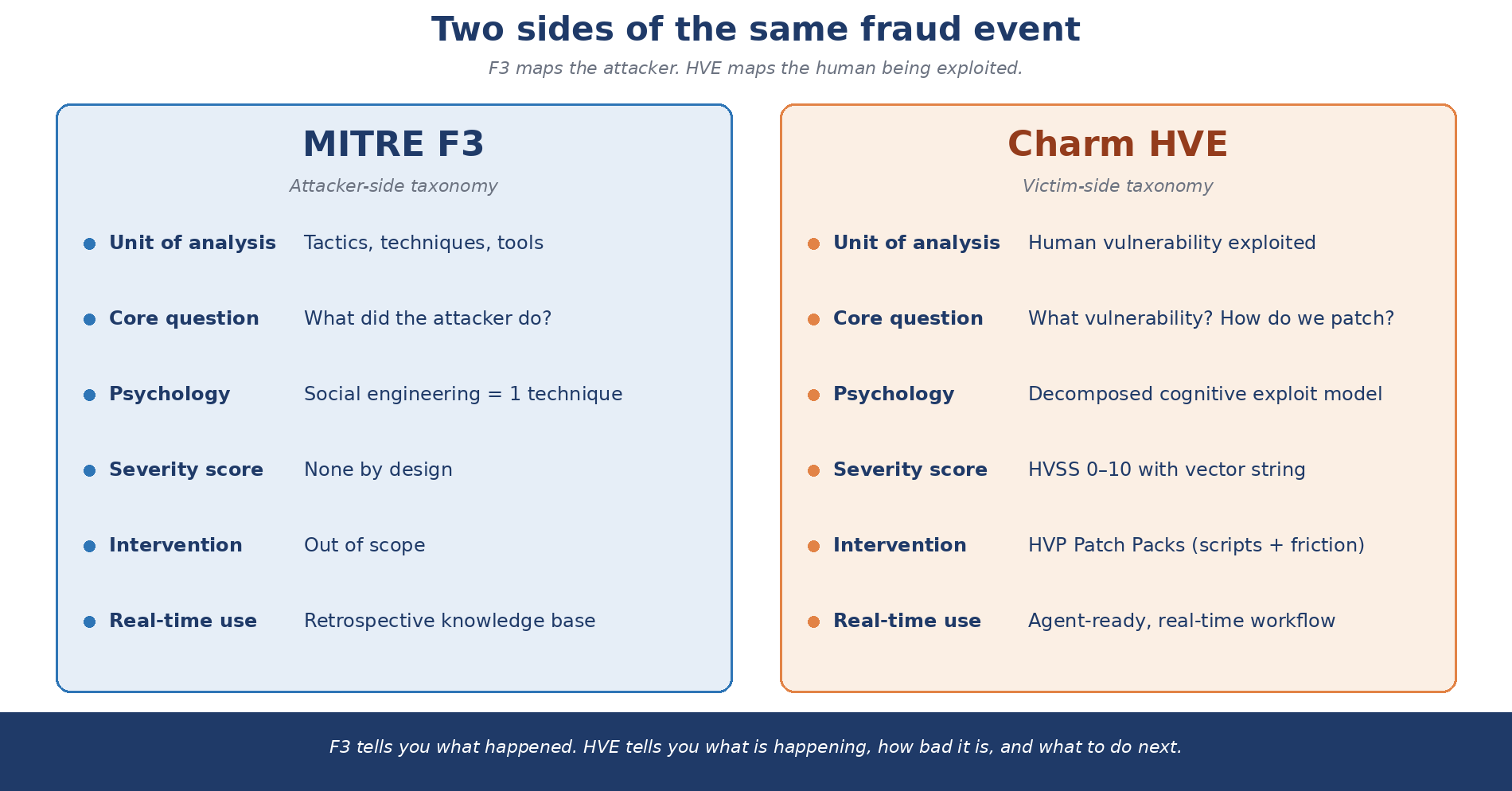
At a high level, HVE adds four things F3 intentionally leaves out:
- A decomposition of any human-centric attack into its cognitive components, scenario, persona, hook, trigger, susceptibility driver, grooming depth, so detection can target the actual exploit, not just the channel.
- HVSS: a 0-10 severity score with an explainable vector string, calibrated for human-targeted attacks. Think CVSS, but for human vulnerability.
- HVP Patch Packs, intervention bundles with calibrated conversational scripts, friction actions, escalation policies, and post-event steps. Threat intelligence becomes an intervention protocol.
- A full lifecycle model: Protection, Prevention, and Remediation, so the framework keeps covering the victim after the attacker has moved on.
Why This Matters Now
Regulators on both sides of the Atlantic are moving toward institutional liability for fraud losses. The UK's APP reimbursement model is already law, similar pressure is mounting across the US, EU, Australia, and Singapore. At the same time, generative AI has collapsed the cost of producing credible phishing, voice cloning, deepfake executives, and multi-channel scam content. The question of whether the industry has a rigorous, machine-readable framework for human vulnerability is no longer academic.
Ultimately, as regulatory liability shifts toward institutions and AI-driven fraud scales exponentially, the adoption of Charm’s HVE is no longer optional, it is the essential operational engine required to manifest the f3 framework into a robust, real-world defense.
© 2026 Charm Security. Preview of forthcoming research. The authoritative reference will be the published HVE framework v1.0.






